- Who are we?
Strategic IT partner
Count on our expertise to accelerate your digitisation
- Maximum partnerships with A+ brands
- Mountains of experience in thousands of environments
- Unrivalled expertise in cybersecurity
- Up to 24/7 monitoring & support
- Core healthy business for +30 years
- +200 Certified employees with passion
- Sober, knowledgeable advice
- Unique puzzle of proven top solutions
From advice until installation, from support until complete relief.
We are ready! - Managed Services
IT Analyses, Consulting, installations...
- NIS-2 Cybersecurity AuditCertified experts uncover every vulnerability
- Applications (Dynamics 365 ERP/CRM, Microsoft 365, Copilot...)Work more efficiently (together) with Dynamics 365 & Microsoft 365, among others
- Licence Audit (Software Asset Management)Are all licences in order? You can often optimise and save a lot!
- General IT Analysis and InstallationsA new look at your environment by our specialists
- Wi-Fi SurveyDetect and fix jammers and hard-to-reach areas
- Solutions
- Events
Accelerate your digitalization.
Get an interactive tour of state-of-the art solutions. - Jobs
Join our team from Turnhout, Houthalen and/or Geel.
You end up in a 'Great Place To Work!'From advice until installation, from support until complete relief.
We are ready! - Customer Area
As a customer, you can manage support tickets, quotes and licences yourself.
Request access via business@vanroey.beNeed a login or request a quote? Contact us via internalsales@vanroey.be | 014 470 600
- Recording
What is Operational Technology (OT) and how can Fortinet secure these environments?
Protect your industrial environment
Lars Putteneers, Channel System Engineer at Fortinet gives an introduction to Operational Technology Security. He explains in 30 minutes how to protect your industrial environment.
- What is OT and how does it differ from IT
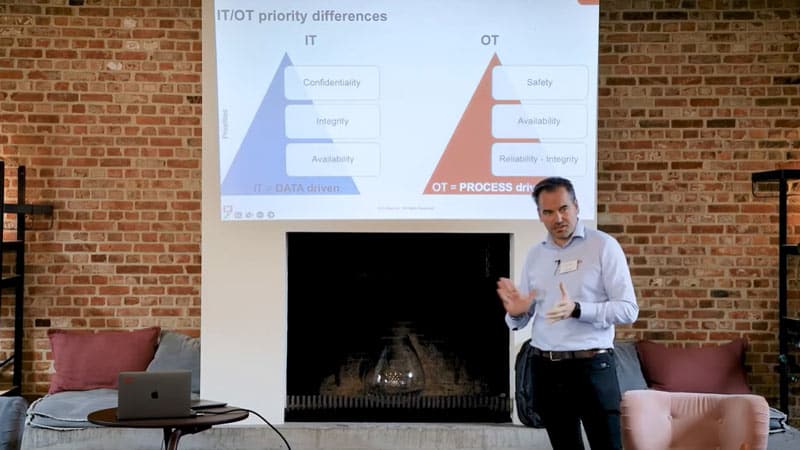
- Difference in priorities between IT & OT
- What are the challenges in protecting OT environments?
- The Purdue model
- Fortinet benefits in terms of OT Security
- Understanding security techniques